[ad_1]
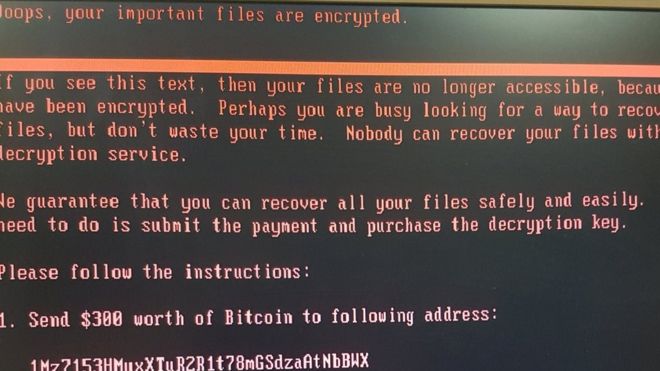
Windows computers around the world are locking up and displaying the stark, black-and-red message you see above in the wake of another major ransomware attack.
This is PetrWrap, a new ransomware tool built from the bones of Petya, which held users’ files for “ransom” and demanded usually egregious payment in exchange for the encryption key earlier this spring. Without getting too deep in the weeds, PetrWrap is essentially a revision on this method that subverts protections put in place following Petya’s outbreak.
According to the BBC, the PetrWrap ransomware has already infected computers within some major national infrastructures and some of the world’s largest institutions. Namely, the Ukranian power company, its central bank and Kiev’s main airport have suffered attacks from the ransomware.
Other victims of note include the Chernobyl nuclear power plant, Danish shipping company Maersk as well as victims in the US, including pharmaceutical firm Merck and the US offices of a law firm known as DLA Piper, The Verge reports.
What is PetrWrap and what does it do?
PetrWrap is essentially a sequel to the Petya ransomware that plagued businesses earlier this spring, wholesale repurposing pieces of it to carry out much of the same function. That is, PetrWrap will find its way into your hard drive and encrypt its files, making them inaccessible without an encryption key that – you guessed it – is within the hands of the hackers.
PetrWrap uses the same EternalBlue exploit employed by WannaCry earlier this spring to spread, targeting Windows computers’ SMB file-sharing system and believed to have been developed by the National Security Administration, or NSA, in the US.
As for how it got here in the first place, the BBC’s resident expert professor Alan Woodward of Surrey University suspects an infected spreadsheet via email as the likely culprit.
While PetrWrap employs the same encryption method as Petya that targets Windows’ Master File Table (MFT) – a record the operating system follows when looking up file destinations – to deny access to all files at once, it builds upon that method with new protections.
According to SecureList, PetrWrap can patch vulnerabilities in Petya that previously made it easy for security firms to restore said data. So, while your antivirus will detect PetrWrap on your system, it’s likely already done its job, making getting your files back will be difficult without paying up.
Even if users were to pay up – and this is something we would not recommend – the hackers behind PetrWrap have since lost access to the email account through which it was sending out encryption keys. Posteo, the German email provider, announced that it has shuttered PetrWrap’s account by blocking access to any address with the word “wowsmith” in it.
So now it is impossible for the the group to read or respond to any messages sent to the address.
How to protect yourself
Sadly, beyond the basic protections we’d recommend anyway, there doesn’t yet seem to be anything specific that can be done to protect your devices from PetrWrap infection. However, let’s run through those basics, so that at least you can enjoy the internet with a bit less of a shroud of paranoia:
- Update your system daily – new security patches come in almost daily
- Activate and update Windows Defender – try setting it to scan regularly, too
- Consider a second anti-virus – it might behove you to pay up for more robust scanning
- Don’t open emails or email attachments from people you don’t know – simple enough
- Don’t open emails or email attachments that look odd, period – would your co-worker send that?
That said, to our knowledge PetrWrap has so far only infected businesses worldwide, not the systems of average consumers. However, regardless of how safe you might think you may be from this attack, the tips above should be followed without question.
Image Credit: BBC
[ad_2]
Source link
